The Invisible Attack Surface: Why METRC, BioTrack, and Seed-to-Sale Platforms Are Cannabis's Most Dangerous Compliance Vulnerability

Every licensed cannabis operator in America is legally required to connect their business to a government-mandated tracking system. Most of them have never thought about what happens when that system — or their connection to it — gets attacked. In 2026, with federal cybersecurity oversight arriving alongside Schedule III reclassification, they're about to find out how expensive that oversight has been.
The Compliance System That Became an Attack Surface
When states began legalizing cannabis, they faced an immediate regulatory challenge: how do you track every plant, every gram, and every transaction in an industry that had operated entirely underground for decades? The answer was seed-to-sale tracking — a state-mandated software layer that logs every single movement of cannabis product from cultivation through retail sale, creating an auditable trail that regulators use to detect diversion, verify tax compliance, and enforce licensing conditions.
Two platforms dominate this landscape. METRC (Marijuana Enforcement Tracking Reporting and Compliance) currently holds contracts in more than 27 states, making it the single most dominant piece of mandatory technology infrastructure in the American cannabis industry. BioTrack — acquired by Forian Inc. — holds contracts in several additional states and was, until early 2026, the primary tracking system for New York's cannabis market before the state's Office of Cannabis Management mandated a migration to METRC.
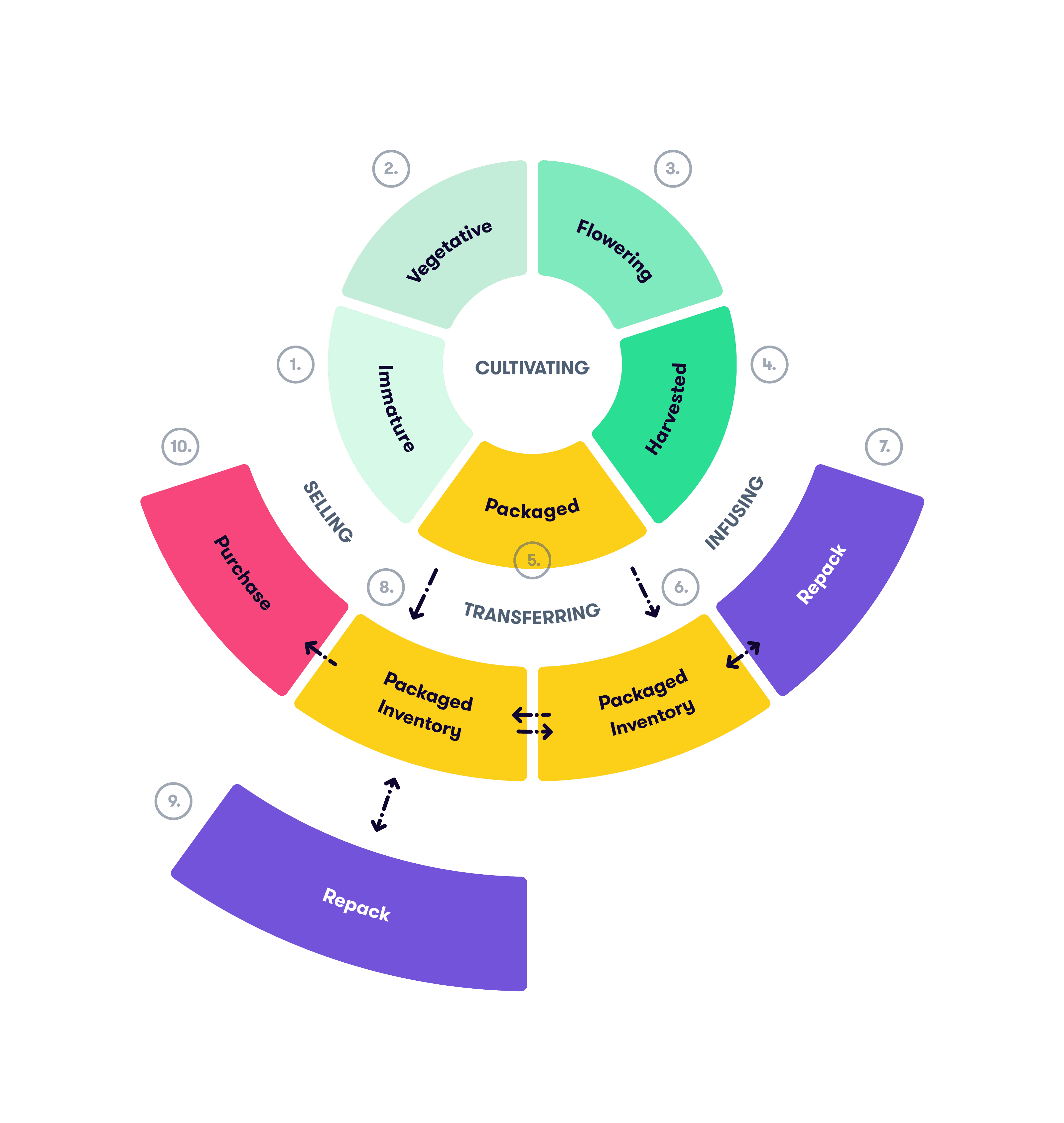
Together, these two platforms are the technical backbone of legal cannabis in America. Every cultivator, processor, manufacturer, distributor, and retailer in a METRC or BioTrack state is required to maintain a live, integrated connection to these systems — reporting plant counts, harvest weights, batch numbers, transfer manifests, and retail sales data in near real-time.
Here is the uncomfortable truth that most operators, regulators, and vendors have avoided confronting: these mandatory compliance systems are among the most attractive and most concentrated attack surfaces in the entire cannabis supply chain. A single successful breach of METRC's infrastructure doesn't expose one dispensary's customer records — it potentially exposes the inventory data, transfer records, and business intelligence of every cannabis operator in every state where METRC holds a government contract. And yet until the federal government began its Schedule III reclassification process, no federal cybersecurity oversight applied to either the platforms themselves or the operators required to use them.
That is about to change. The operators who understand the attack surface they've been sitting on — and build toward the federal security standards now arriving — will be the ones who survive what's coming.
The Washington State Hack: A Preview Nobody Acted On
The seed-to-sale platform vulnerability isn't a theoretical risk. It has already materialized — and the cannabis industry's collective response was to move on and forget about it.
In February 2018, Washington State's cannabis traceability system — operated by MJ Freeway — was hacked. The attackers didn't just steal data; they actively manipulated it. An intruder breached the system and downloaded a copy of the traceability database — which contained delivery route information, transportation manifests, delivery-vehicle specifications including license plate numbers and VINs, for four days of cannabis deliveries across the entire state.
The operational implications were severe: the hack disrupted transfer and manifest data statewide, creating compliance chaos for every operator in Washington's regulated market. The Washington State Liquor and Cannabis Board brought in the State Office of Cybersecurity to investigate. And crucially — cannabis businesses were not notified of the attack until five days after the breach was discovered, because of agency notification protocols that prioritized internal investigation over operator awareness.
This was not MJ Freeway's first incident. In the years prior to the Washington breach, the company had suffered repeated attacks, and source code for its software had been posted online by attackers. The company's security posture was broadly understood to be inadequate — and yet it remained the mandatory compliance infrastructure for multiple state cannabis markets because switching costs were high and regulatory processes moved slowly.
The Washington 2018 incident established three principles that remain painfully relevant in 2026:
- Seed-to-sale platforms are high-value targets precisely because they hold aggregated data for all operators in a state simultaneously
- Government notification protocols after a breach of mandatory compliance infrastructure routinely fail to protect operators from operational damage
- The mandatory nature of these platforms creates a captive customer base with no ability to opt out of a vendor whose security posture they have serious concerns about
Eight years later, these principles remain unaddressed at the systemic level.
The METRC Whistleblower: Systemic Accountability Failures at the Core
In April 2025, a federal whistleblower lawsuit against METRC revealed something that regulators, operators, and compliance professionals across 27 states needed to hear — and that most of them haven't fully processed yet.
Marcus Estes, a former METRC Executive Vice President who joined the company following its 2023 acquisition of his blockchain tracking firm Chroma Signet, filed suit alleging that METRC was knowingly failing to flag irregularities in its tracking data despite explicit contractual obligations to do so. The lawsuit, filed in connection with related actions by Catalyst Cannabis Company in California, alleged that METRC possessed the technical capability to identify patterns consistent with illegal diversion — including "burner distros," operations that legally acquire cannabis through licensed California businesses and then divert substantial quantities into illegal interstate markets — but was choosing not to flag them.

The lawsuit alleged that the reason for this deliberate non-reporting was commercially motivated: METRC's primary revenue stream is the sale of proprietary RFID tracking tags that every cannabis plant and package must carry. Moving toward the more secure, less expensive QR-based tracking technology that Estes had developed would have undermined that revenue stream. Estes claimed that when he raised these compliance failures internally, METRC retaliated by marginalizing him and ultimately terminating his employment without cause.
METRC holds a $40 million annual contract with California alone that contractually required the company to flag irregularities in tracking data. The allegations suggest that those obligations were not being met — while every licensed cannabis operator in 27 states operated under the assumption that their mandatory compliance infrastructure was functioning as designed.
For the cybersecurity implications of this lawsuit, the critical issue is not just whether illegal diversion was occurring — it's what the allegations reveal about the accountability gap at the center of seed-to-sale compliance infrastructure. If the dominant tracking platform in American cannabis was allegedly choosing not to exercise its own data monitoring capabilities for commercial reasons, operators have been assuming a level of system integrity that may not exist. Their compliance posture — which depends on the accuracy and security of their METRC or BioTrack data — has been built on a foundation whose integrity is now the subject of active federal litigation.
New York's BioTrack-to-METRC Migration: A Security Crisis in Motion
In early 2026, New York's Office of Cannabis Management mandated a statewide migration from BioTrack to METRC for all cannabis operators — a compliance event that, from a cybersecurity perspective, represents one of the most significant data security risks any state cannabis market has created in years.
The migration requires every New York cannabis operator to:
- Export and back up all BioTrack inventory, transfer, and compliance data before cutover deadlines
- Simultaneously maintain operational reporting in BioTrack during the transition window
- Migrate historical data into METRC's architecture while maintaining continuity of real-time reporting
- Reconfigure or replace every POS integration, ERP connection, and compliance workflow that was built around BioTrack's API
From a security standpoint, system migrations are among the highest-risk operational events a business can undergo. The specific risks in the New York context include:
Data integrity corruption during migration — historical compliance records that don't migrate cleanly create regulatory discrepancies that can trigger enforcement action, license suspension, or audit demands even when the underlying business was operating compliantly.
Expanded API attack surface during dual-system operation — during the transition window, operators run live connections to two separate tracking systems simultaneously. Every additional API connection is an additional potential attack vector, and security teams are typically focused on making the migration work rather than monitoring for intrusions across doubled system complexity.

Phishing campaigns targeting the migration — attackers routinely exploit major compliance events to launch highly credible phishing campaigns. A fake "METRC account verification" email sent to New York cannabis operators during the migration window — with urgency around missing cutover deadlines — is exactly the kind of social engineering that succeeds against compliance-focused staff under pressure.
Third-party integration vendor risk during reconfiguration — every POS vendor, ERP provider, and compliance software company serving the New York market is simultaneously rebuilding their METRC integrations. Any of these vendors introducing vulnerabilities into their METRC API connections during the reconfiguration period creates risk that flows to every one of their cannabis operator clients.
New York cannabis operators who have not explicitly addressed these migration-specific security risks in their incident response and change management procedures are operating blind through one of the highest-risk periods their compliance infrastructure will ever face.
The API Integration Layer: Where Operator Data Lives and Dies
Every licensed cannabis operator using METRC or BioTrack connects to these systems through APIs — application programming interfaces that allow POS systems, inventory management platforms, and ERP software to automatically report data to the state tracking system without manual entry.
This API layer is where the security risk to individual operators is most acute — and most poorly understood. A few critical facts about the METRC API architecture that every operator should know:
API keys are the keys to your compliance kingdom. Your METRC API key authenticates every automated data submission from your POS or inventory system. If that key is compromised — through a phishing attack on a staff member, a breach of a POS vendor's systems, or improper key management practices — an attacker gains the ability to manipulate your METRC data: falsifying inventory counts, creating phantom transfers, deleting plant tags, or corrupting batch records in ways that create severe compliance discrepancies.

Compromised METRC data is a license threat, not just a security incident. Under every state cannabis licensing framework that mandates METRC or BioTrack, operators are legally responsible for the accuracy of their tracking data. If an attacker manipulates your METRC inventory to show missing product — or creates transfer records that don't match physical shipments — the operator faces regulatory action for compliance failures that were actually the result of a cyberattack. Distinguishing between an operator's deliberate diversion and a cyberattack-induced data manipulation is an investigation that takes months, during which your license can be suspended.
Third-party POS integrations multiply the API attack surface. The METRC API terms require that any third-party software integrating with METRC must be a licensed METRC API partner. However, the security standards applied to these partner integrations vary enormously. A POS vendor with 200 dispensary clients, each authenticated through the vendor's own API management layer, creates a single point of failure that — if compromised — simultaneously exposes all 200 operators' METRC connections.
Cannabis-specific phishing specifically targets METRC credentials. Security researchers have documented phishing campaigns sending fake "METRC account verification required" emails to cannabis operators — emails that mimic the visual design of legitimate METRC communications and direct staff to credential-harvesting pages. These attacks work because METRC compliance is genuinely urgent, deadlines are real, and the consequences of a missed reporting deadline are severe enough that many dispensary employees will click before they verify.
Federal Oversight Arrives: What Schedule III Means for Seed-to-Sale Security
The cannabis industry has operated under a simple reality for its entire legal existence: state-level compliance requirements, but no federal cybersecurity oversight. Seed-to-sale platforms were required by states, but no federal agency set the security standards those platforms had to meet. Operators were required to connect to these systems, but no federal regulation dictated how they had to secure those connections.
That changes with Schedule III reclassification. Once cannabis moves to Schedule III, a cascade of federal compliance frameworks begins applying to cannabis operators for the first time:

DEA CSOS integration implications — Schedule III cannabis operators entering the federal controlled substance ordering system will be required to ensure that their seed-to-sale data is compatible with DEA CSOS reporting requirements. The security standards for CSOS — PKI certificates, cryptographic signatures, tamper-evident records — will need to integrate with or overlay the existing METRC/BioTrack infrastructure. There is currently no roadmap for how METRC or BioTrack will achieve this integration.
FTC Safeguards Rule obligations — operators gaining banking access under Schedule III will be subject to the FTC's Safeguards Rule implementing GLBA, which requires formal risk assessments, documented security programs, and vendor oversight for all systems handling financial data — including POS systems integrated with METRC.
HIPAA for medical operators — medical cannabis dispensaries that gain formal healthcare provider status under Schedule III face HIPAA Security Rule requirements for electronic protected health information, which includes any health-related data passing through seed-to-sale systems.
State breach notification obligations overlaid with federal requirements — when a METRC or BioTrack connected system is breached, the notification obligations now potentially span state cannabis regulators, state data protection authorities, federal health authorities, and financial regulators simultaneously. Cannabis operators who don't have multi-jurisdictional breach notification protocols in place before this happens will be building the plane while it's crashing.
The specific challenge for seed-to-sale security under federal oversight is that METRC and BioTrack were not built to federal compliance standards. They were built to satisfy state cannabis regulatory requirements — which historically had no cybersecurity component. The arrival of federal oversight creates a scenario where the mandatory compliance infrastructure that operators are required to use may not meet the federal standards that operators are now required to satisfy. Operators sit in the middle of that gap, exposed from both directions.

The Operator's Responsibility: What You Control When the Platform Doesn't
It would be easy to read this article as an argument that seed-to-sale security is METRC's or BioTrack's problem to solve. It is not. The regulatory and legal reality is that operators are responsible for their compliance data regardless of which platform stores it.
Here is what every cannabis operator with a seed-to-sale mandate can and must control right now:
API Key Management
Treat your METRC and BioTrack API keys with the same security discipline you would apply to banking credentials. Keys should be stored in encrypted secret management systems, never hardcoded into scripts or application code, rotated on a regular schedule, and immediately revoked if there is any reason to believe they were exposed. Each integration should use the minimum permission scope necessary — a key used for inventory reporting should not carry transfer authorization permissions.
Third-Party Integration Vendor Vetting
Every POS system, ERP, and inventory management platform connecting to METRC or BioTrack on your behalf must be held to explicit security standards as a contractual condition of your vendor relationship. At minimum, require SOC 2 Type II attestation, documented API security practices, and contractual breach notification obligations of no more than 24 hours. The vendor's API key management practices should be part of your onboarding due diligence.
Daily Compliance Data Backups
Your METRC and BioTrack data should be backed up daily to offline, encrypted storage that is disconnected from your live network. In a ransomware scenario — or in the event that a platform outage corrupts your reporting data — your ability to reconstruct accurate compliance records from backup is the difference between a manageable incident and a regulatory crisis. In 2025, nearly 98% of ransomware cases involved attackers specifically targeting and attempting to destroy backup systems.
Migration Change Management
For New York operators undergoing the BioTrack-to-METRC migration, and for any operator facing a platform transition in their state: treat every migration as a security-critical event with its own change management protocol, dual-system monitoring, and phishing awareness campaign for all staff involved in the transition.
Documented Incident Response for Compliance System Breaches
Your incident response plan must specifically address the scenario where your seed-to-sale connection is compromised. This means: who contacts state cannabis regulators (and within what timeframe), how do you reconstruct compliance records from backups, how do you document that discrepancies were caused by a cyberattack rather than operational errors or diversion, and which legal counsel is on call for regulatory defense.
Phishing Training Focused on METRC/BioTrack Social Engineering
Your staff must know that fake METRC compliance emails are a documented attack vector. Regular training that includes simulated cannabis-specific phishing scenarios — regulatory urgency, compliance deadline pressure, platform account verification — is a direct mitigation for the most common initial attack vector your seed-to-sale connected systems face.
The Bottom Line
METRC and BioTrack are not just software platforms. They are the mandatory compliance nervous system of the entire American cannabis industry — centralized repositories of aggregated production, transfer, and sales data that represent one of the most concentrated attack surfaces in any regulated industry in the country. The Washington State hack proved in 2018 that this attack surface is real and exploitable. The METRC whistleblower lawsuit in 2025 proved that the accountability mechanisms governing this infrastructure have systemic gaps. And the Schedule III reclassification arriving in 2026 proves that federal cybersecurity standards are coming to an industry that built its compliance infrastructure without them.
Operators who wait for METRC, BioTrack, or state regulators to solve the seed-to-sale security problem for them are waiting for something that may never arrive — or that will arrive only after a breach has already made the cost of that wait catastrophically clear. The security controls that protect your compliance data are within your control right now. The question is whether you'll exercise that control before the federal oversight clock runs out — or after.
cannasecure.tech provides seed-to-sale security assessments, API key management programs, vendor security due diligence frameworks, and federal compliance readiness evaluations for cannabis operators across all METRC and BioTrack states. Contact us before your compliance infrastructure becomes your biggest liability.











